A while back we’ve seen how Avast monetizes their users. Today we have a much smaller fish to fry, largely because the Avira’s extensions in question aren’t installed by default and require explicit user action for the additional “protection.” So these have far fewer users, currently 400 thousands on Firefox and slightly above a million on Chrome according to official add-on store numbers. It doesn’t make their functionality any less problematic however.
That’s especially the case for Avira Browser Safety extension that Avira offers for Firefox and Opera. While the vendor’s homepage lists “Find the best deals on items you’re shopping for” as last feature in the list, the extension description in the add-on stores “forgets” to mention this monetization strategy. I’m not sure why the identical Chrome extension is called “Avira Safe Shopping” but at least here the users get some transparency.
Contents
Summary of the findings
The Avira Browser Safety extension is identical to Avira Safe Shopping and monetizes by offering “best shopping deals” to the users. This functionality is underdocumented, particularly in Avira’s privacy policy. It is also risky however, as Avira chose to implement it in such a way that it will execute JavaScript code from Avira’s servers on arbitrary websites as well as in the context of the extension itself. In theory, this allows Avira or anybody with control of this particular server to target individual users, spy on them or mess with their browsing experience in almost arbitrary ways.
In addition to that, the security part of the extension is implemented in a suboptimal way and will upload the entire browsing history of the users to Avira’s servers without even removing potentially sensitive data first. Again, Avira’s privacy policy is severely lacking and won’t make any clear statements as to what happens with this data.
Update (2019-12-19): Avira reached out to me to discuss the issues. You can find a summary of their clarifications at the bottom of this post.
How does this monetization approach work?
You’ve probably seen some of the numerous websites offering you coupon codes for certain shops to help you get the best deal. Or maybe you’ve even used browser extensions doing the same. If you ever asked yourself what these are getting out of it: the shop owners are paying them for referring customers to the shop. So even if you already were at this shop and selected the product you wanted to buy, if you then wandered off to a coupon deal website and had it send you back to the shop – the owner of the coupon deal website gets paid a certain percentage of your spending.
And that’s the reason why users of Avira Browser Safety, having installed that browser extension for protection, will occasionally see a message displayed on top of a website. Whenever some user takes advantage of the offers, the shop owners pay Avira. Not directly of course but via their partner Ciuvo GmbH which appears to provide the technology behind this feature.
Why is this feature problematic?
Monetizing a product in this way isn’t unusual. Ciuvo has their own browser extension sharing some code with Avira’s. And a bunch of other antivirus vendors also offer shopping extensions, without these being considered problematic as long as users install them by choice. However, Avira for some reason decided that they want full control over this feature without having to release a new extension version. So whenever the extension asks https://offers.avira.com/aviraoffers/api/v2/offers for a list of deals, the response contains a JavaScript URL among other things.
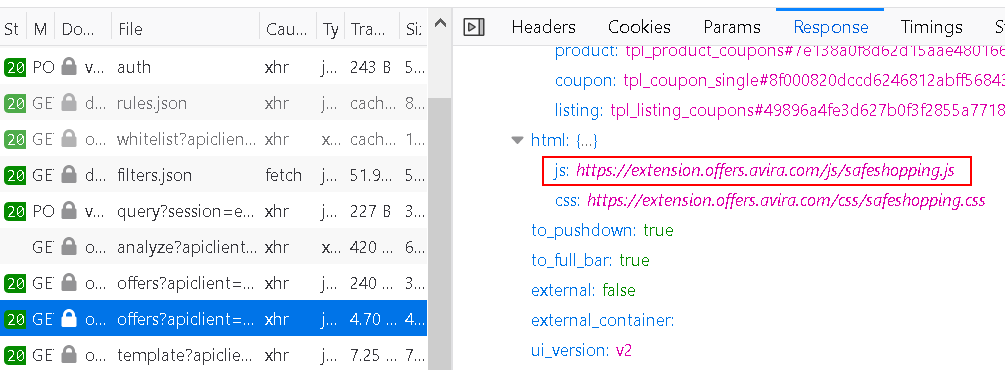
What does the extension do with this script? It runs it in the context of the extension where it can do anything that the extension can do (meaning: “Access your data for all websites”). Mind you, this functionality is specific to Avira, Ciuvo’s own browser extension gets along without it just fine.
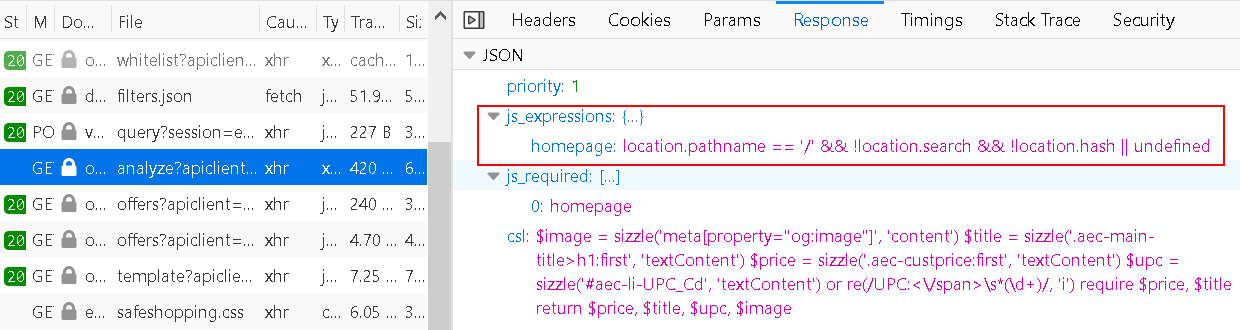
It’s not just that. Before the extension requests offers, it analyzes the page. The rules for performing this analysis are also determined by the server when responding to https://offers.avira.com/aviraoffers/api/v2/analyze request. The response contains a list of “JS expressions” which is essentially that: JavaScript code to be run in the context of the page, again functionality missing from the Ciuvo extension.
And how are the websites selected where these actions have to be performed? They are also determined by the Avira server of course, every now an then the extension will download a huge list from https://offers.avira.com/aviraoffers/api/v2/whitelist.
The end result is: Avira decides what websites this extension should mess with and it decides how the extension should mess with them. And while functionality in the released extension applies to all users, Avira (or anybody taking control of offers.avira.com) could target individual users to ship a malicious payload to them. In fact, they could even change the extension functionality completely, e.g. turning it into spyware or adware – but only for users in Brazil, so that it doesn’t get noticed. That’s a whole lot of trust to ask for, and it makes Avira infrastructure a very valuable hacking target.
Let’s talk about privacy
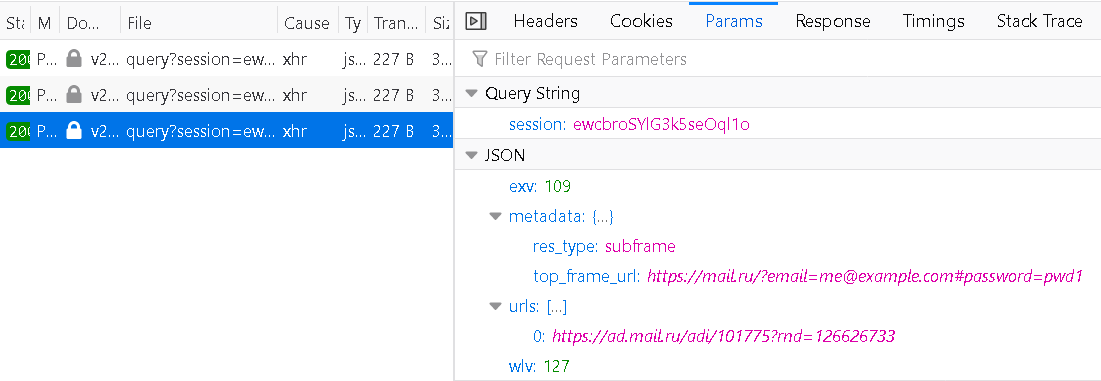
Even if you ignore the fact that Avira can repurpose this extension at any time, there is the question of privacy. In the process of “page analysis” the extension collects and transmits considerable amounts of data. You can see the script guiding this data collection as csl in the image above. Typically, it will extract the description of the product you are looking at as well as pricing information. Is there maybe some price comparison service out there running on this data? However, it will also transmit your Google search query for example if the search produces shopping results. All that data is being accompanied by a random albeit persistent user identifier.
Having access to that much data, Avira will certainly have a well-written privacy policy? Actually, the first challenge is finding it: Avira Browser Safety listing on Mozilla Add-ons doesn’t even link to the privacy policy. And while this privacy policy has individual sections for various products, Avira Browser Safety isn’t listed. But the identical Avira Safe Shopping extension is listed, so we can check there:
If you use Avira Safe Shopping, it is part of our contractual obligation to present you with suitable products from other providers or other providers’ conditions for the same product. Data processing is done exclusively in accordance with the performance of the contract.
Does this mean that Avira doesn’t store any of this data whatsoever? I’d certainly hope so, but I’m not sure that this is the meaning. Also, why send a user identifier along if you don’t keep the data?
There is also the question about what data third parties receive here. For example, if you select a coupon on the website displayed above you first get sent to https://offers.avira.com/aviraoffers/api/v2/tracker (no, doesn’t sound like Avira isn’t keeping any data) which redirects you to ciuvo.com which redirects you to savings.com which (after setting lots of cookies) redirects you to pjtra.com which redirects you to pepperjamnetwork.com which (after also setting lots of cookies) finally sends you back to the shop. For other websites you will see other redirect chains involving other companies.
And what about browsing history data?
There is also the actual security part of the extension, preventing you from visiting malicious websites. In order to decide which website is malicious it sends requests to https://v2.auc.avira.com/api/query. In the process it uploads your entire browsing history, along with any potentially sensitive URL parameters. While the session parameter seen here is temporary, a session is created by requesting https://v2.auc.avira.com/api/auth with a persistent user identifier, so in principle the entire browsing history for any user can be reconstructed on the server side.
There are two factors that distinguish this from the Avast case and make this look like lack of concern rather than outright spying. First, there is no context information being collected here. And second, the server responses are cached to some degree, so visiting a website won’t always result in a request to Avast servers.
Still, Avira would be well-advised to at least remove query and anchor parts from the addresses. Also, their privacy policy needs clear statements on how this data is processed and whether any of it is being retained.
Conclusions
The excessive data collection, incomplete privacy policy, unexpected functionality and execution of remote code are all issues that violate Mozilla Add-ons policies. I notified Mozilla and I assume that they will ask Avira to fix these. Maybe the Firefox extension will even be renamed to match the one for Chrome?
Update (2019-12-12): As of now, Avira Browser Safety extension is no longer listed on Mozilla Add-ons. I did not receive any reply from Mozilla yet other than “we are looking into this.”
I did not report any of this to Google, none of these issues have been considered a concern in the past. In particular, Google allows execution of remote code as long as there is no proof for it being used for malicious purposes. But I hope that Avira will improve their Chrome extension as well nevertheless.
Avira’s clarifications
Update (2019-12-19): Avira reached out to me with some clarifications about this functionality and the intent behind it. Here is my summary of the communication:
- The “Browser Safety” extension is in the process of being renamed into “Safe Shopping.” This is only complete for Chrome so far but the plan is to rename the variants for other browsers as well. Incomplete add-on store descriptions and privacy policy are partly a side-effect of this transitional state.
- The data received by Avira servers might only be stored temporarily for debugging purposes, no longer than 14 days for the shopping functionality and no longer than 7 days for the security component.
- Avira does not attempt to reconstruct browsing histories, create user profiles or deduce any kind of behavior patterns. The user identifier is only used for basic statistics, and the data is never shared with any third parties.
- The potential value of the data is intentionally being restricted by aggressive caching and whitelisting of a number of popular services.
- None of the extension data is transmitted to coupon providers.
- Running remote JavaScript code was indeed meant to provide more flexibility to Avira, this functionality will be removed however.
- Considering query parameters is important when making decisions to block malicious content. These allow in particular identifying ad campaigns, malicious redirects and specific resources on websites like Google Drive. Similar services like Google Safe Browsing and Microsoft SmartScreen also transmit query parameters.
Comments
Thanks for the article which is about Avira, I removed Avira Browser Safety. You said about F-Secure that it is "pretty solid" , do you mean it is awesome? Do you think using F-Secure Online Scanner is a good idea? https://www.f-secure.com/en/home/free-tools/online-scanner Thank You.
No, I did not mean "awesome" - so far no antivirus software was really convincing. In general, it's best to keep them out of your browser, the value they are adding there is negligible.
Hi Wladimir,
I work for Avira, and we're taking privacy matters very seriously. We do not sell user data, also not in anonymized form, all data is used for security purposes. We are trying to reach out to you and clear up some of the items you have reported.
Feel free to reach back with the contact provided and I'll gladly setup a call to go through them.
Marcus Koenig, VP Protection @ Avira
I do not think that you sell data, and that's reflected in the post. It rather looks like some sloppy practices. I'll happily correct any details if I got them wrong here.
Ok, I guess, I am good with all what I have now, these extensions: Adblock ultimate, Adblock Plus, AdGuard Blocker, and I have Avira and Adguard installed on my pc, I am hope I am fully protected. Thank You.
Yes, instead they should have secretly pushed a default enabled "option" to people that would allow third parties to data mine browsers to profit the extension developer.